The Case for Multi-Person Authorization

Do you need yet another security control? Most organizations have added zero-trust principles as the driving strategy for their security posture. But should one person have the ability to change settings that could hinder your organization's ability to recover from a cyber incident? The answer is obviously no.
This is where multi-person authorization (MPA) comes in and why it has emerged as a critical control to support cyber resilience.
The cyber resilience focus has moved from disaster recovery to ransomware, which now represents the most urgent threat. Globally, 65% of organizations in our recent “Data Risk Management” study report having experienced ransomware attacks in the last two years. These weren’t harmless attacks that were identified and thwarted. These were incidents in which an attacker gained direct entry or access to the targeted system. It takes only one successful attack to do untold damage, ultimately highlighting the extent of threat.
Cyber resilience has two foundational components:
Cybersecurity helps withstand ongoing threats.
Cyber recovery ensures rapid and reliable recovery from destructive events, particularly ransomware attacks.
Without reliable cyber recovery, even the most comprehensive security measures can’t remediate a ransomware or destructive attack. It is not a matter of if an attacker succeeds but when. This is where MPA plays a critical role. Think of MPA in the same way that it takes two people with separate keys to open a bank vault or safety deposit box. MPA prevents an individual from unilaterally changing critical data backup setting and retention periods. This safeguard ensures that you have critical data to resume operations.
Credential theft is a significant threat to backup data and setting. Threat actors use tactics like social engineering and advanced persistent techniques to impersonate privileged users, gaining control over the cyber recovery platform. With this control, they can modify critical settings such as backup schedules, retention levels, and backup deletions, rendering the functions ineffective and putting your organization at the mercy of ransomware demands.
Whether it’s an external threat actor, such as a ransomware gang, or a disgruntled insider, permitting unilateral changes poses a significant threat. Zero-trust principles, featuring multifactor authentication, role-based access controls, and privileged user management, offer substantial protection against this threat. This is also where MPA comes into play.
With the announcement of the Veritas 360 Defense architecture, Veritas has added MPA to control critical settings that threat actors could exploit to delete backup data or change platform settings. Deleting or changing backup platform settings can limit your recovery options, leaving you vulnerable to ransomware demands.
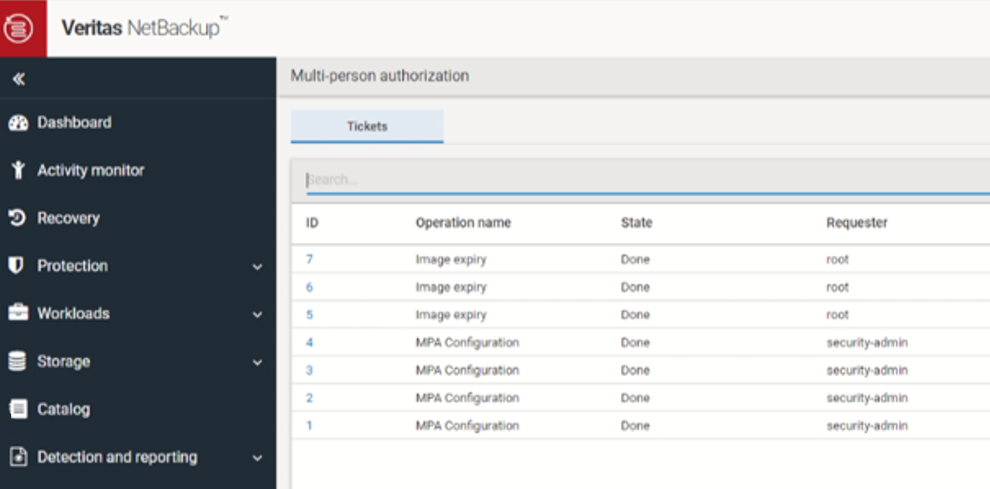
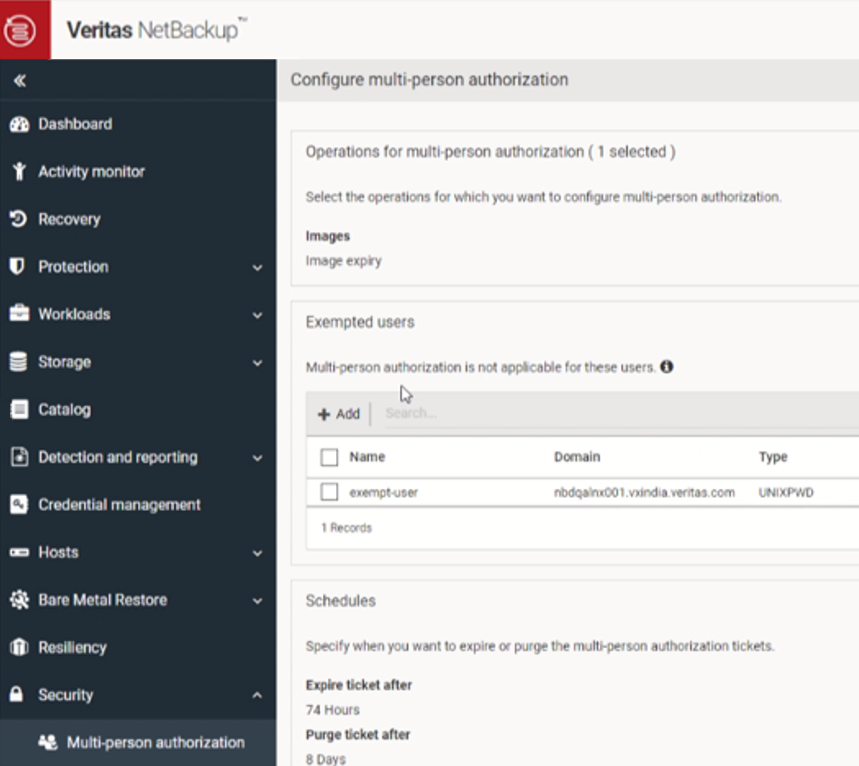
You can configure the MPA capability to support two or more approvers. It also introduces an advanced ticketing system with request details and approver comments for audit and tracking purposes. Examples of functions where Veritas MPA will provide additional protection and layering of security controls (such as multi-factor authentication and role-based access controls) include the deletion of instances, expiration settings of backups, and access to root-level control such a IPMI and SSH.
When enabled, the following operations will require multi-person authorization:
Deletion or expiry of images
Root access for privileged operations while performing advanced-level troubleshooting
Deletion of instances on backup appliances such as NetBackup Flex Appliances
MPA adds an additional layer of protection to the existing enterprise and compliance mode protection. Wherever we find it necessary, Veritas is mandating MPA as per CISA Security by Default guidelines. As an example, deletion of instances on NetBackup Flex Appliance will require mandatory MPA.
Make MPA part of your cyber-recovery security controls to add another layer of zero-trust protection. Ensure your organization has the data it needs to resume operations when a ransomware or destructive event occurs.
Veritas MPA is available now with NetBackup 10.3.