Veritas Cyber Strategy—Secure by Default

At Veritas, we are committed to giving you the control you need to secure your data. I shared what we mean when we say our solutions are Secure by Design in a previous post. Now I want to cover what makes our products Secure by Default.
We aim to keep the world's data available, protected, properly governed — or simply "safe." We do that in the most complex operating environments and the most regulated firms. We work with the same organizations that create and maintain the world's most important critical infrastructure.
Our solutions must be secure when you deploy them, without additional cost. You heard me right: I said cost. Because when a vendor gives you a long checklist of "what you need to do to secure your infrastructure," they’re passing cost along on to you. We want to eliminate that.
Rather than spend additional resources to configure and implement security measures after you’ve deployed the product, you can leverage the built-in security features from the start. This reduces development time and minimizes the need for post-deployment security updates, patches, and costly security incidents.
Before we dive in, I also want to be more forward-looking with a prediction. We already do and will continue to encourage you to implement these security measures. We’ll remind you, nudge you in the right direction, change the defaults for new installations, and occasionally resort to gentle nagging. And when you need a little extra time, we’ll give you a grace period to prepare for change. All at no extra charge.
Now, let's dive into some work that we’ve done to ensure that our solutions are Secure by Default.
Encryption
- Veritas offers data-in-transit encryption (DTE) to protect operations including:
- Data flow from a client to a media server
- Data flow from a media server to a client
- Metadata transfer from a media server to the primary server
- Data flow from one media server to another during duplication and synthetic backup
New installations of Veritas NetBackup and Veritas Alta™ Data Protection will have DTE enabled by default to ensure the security of your data.
Immutable Storage
Veritas provides immutable storage on-premises on hardened appliances and in the cloud. We support end-to-end data immutability on the broadest set of storage platforms, including hardened Veritas Backup Appliances.
Immutability from Veritas is multi-layered and fully present in the backup catalog, storage APIs, and the security controls for access control from a network, user, and system perspective. Appliances feature a secure storage clock and controls to prevent unauthorized access to data, even by fully privileged administrators. Cohasset Associates has assessed Veritas NetBackup compliance with:
- SEC 17 CFR 240-17a-4(f)
- FINRA Rule 4511(c)
- CFC 17 CFR 1.31(c)-(d)
Veritas also supports immutability in the cloud or on-premises backups to enable an air-gapped copy administered by a third party with strong access controls.
Reporting
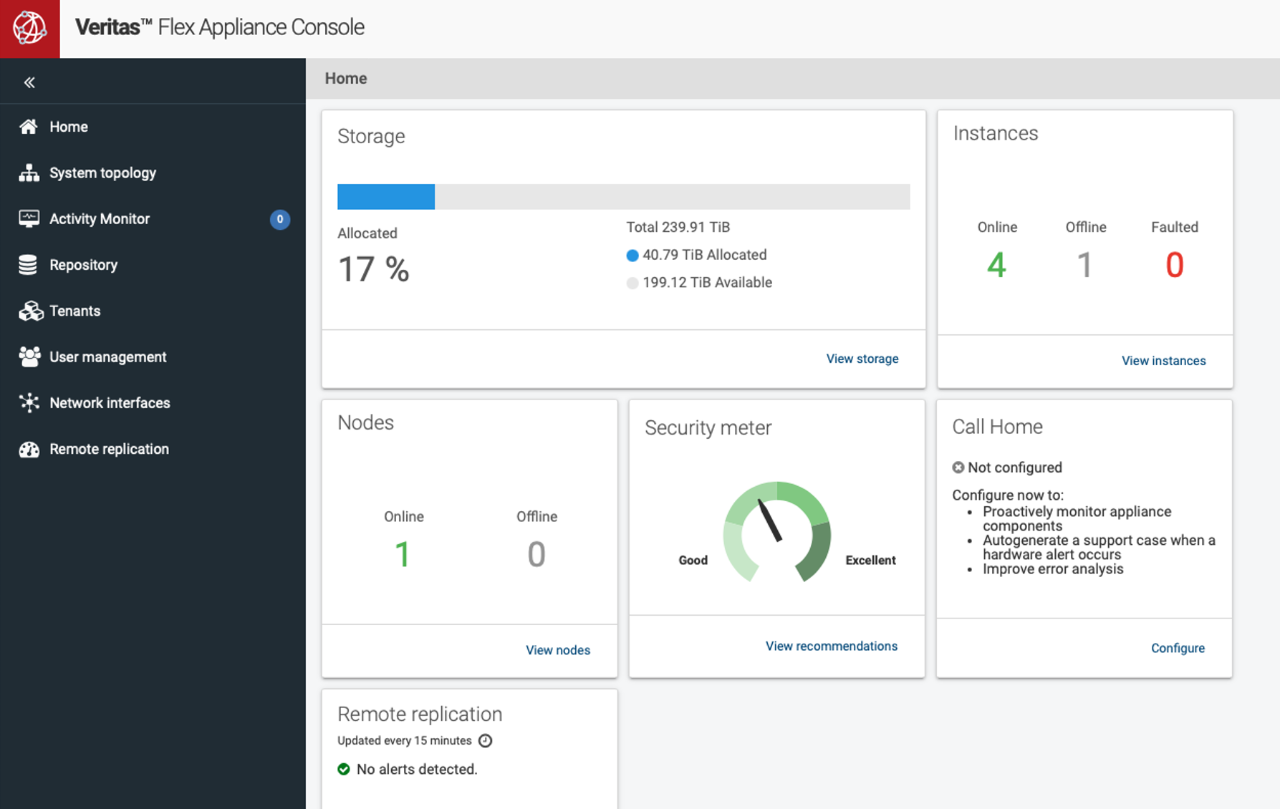
Veritas provides behavioral anomaly detection to provide early indicators of risky behavior. You can leverage user risk scores to assess potential threats and protect against theft or damage. We have also added a ransomware report card and a security meter directly into our products to simplify securing your data.
Authentication
In today’s era, many malicious attackers log in with legitimate stolen credentials. To guard against that, multifactor authentication (MFA) and multi-person Authorization (MPA) will start to be mandatory for new installations. We’ll provide easy on-ramps to secure your data-protection infrastructure when you upgrade.
Common sense and best practice demand that you take basic protections to ensure the confidentiality, integrity, and availability of your data. It’s time to make changes to protect your backups and prepare for confident recoveries with our cyber-resilient capabilities.
Learn more about how Veritas is committed to safeguarding your data at our Veritas Trust Center: Security | Veritas
